CCNA Security Chapter 5 Exam Answers
-
Which two benefits does the IPS version 5.x signature format provide over the version 4.x signature format? (Choose two.)
- support for IPX and AppleTalk protocols
- addition of signature micro engines
- support for comma-delimited data import
- support for encrypted signature parameters*
- addition of a signature risk rating*
-
Which type of IPS signature detection is used to distract and confuse attackers?
- honeypot-based detection*
- policy-based detection
- pattern-based detection
- anomaly-based detection
-
Which statement is true about an atomic alert that is generated by an IPS?
- It is an alert that is used only when a logging attack has begun.
- It is a single alert sent for multiple occurrences of the same signature.
- It is an alert that is generated every time a specific signature has been found.*
- It is both a normal alarm and a summary alarm being sent simultaneously at set intervals.
-
A system analyst is configuring and tuning a recently deployed IPS appliance. By examining the IPS alarm log, the analyst notices that the IPS does not generate alarms for a few known attack packets. Which term describes the lack of alarms by the IPS?
- true negative
- false positive
- false negative*
- true positive
-
A security specialist configures an IPS so that it will generate an alert when an attack is first detected. Alerts for the subsequent detection of the same attack are suppressed for a pre-defined period of time. Another alert will be generated at the end of the period indicating the number of the attack detected. Which IPS alert monitoring mechanism is configured?
- composite alert
- atomic alert
- correlation alert
- summary alert*
-
What information must an IPS track in order to detect attacks matching a composite signature?
- the total number of packets in the attack
- the attacking period used by the attacker
- the network bandwidth consumed by all packets
- the state of packets related to the attack*
-
What is a disadvantage of a pattern-based detection mechanism?
- The normal network traffic pattern must be profiled first.
- It cannot detect unknown attacks.*
- It is difficult to deploy in a large network.
- Its configuration is complex.
-
What is the purpose in configuring an IOS IPS crypto key when enabling IOS IPS on a Cisco router?
- to secure the IOS image in flash
- to enable Cisco Configuration Professional to be launched securely
- to encrypt the master signature file
- to verify the digital signature for the master signature file*
-
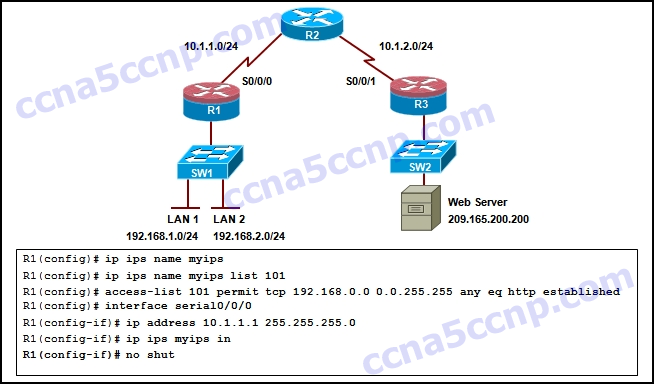
Refer to the exhibit. What is the result of issuing the Cisco IOS IPS commands on router R1?

CCNA Security Chapter 5 Exam Answer v2 001
- All traffic that is permitted by the ACL is subject to inspection by the IPS.*
- A named ACL determines the traffic to be inspected.
- All traffic that is denied by the ACL is subject to inspection by the IPS.
- A numbered ACL is applied to S0/0/0 in the outbound directio
-
In configuring a Cisco router to prepare for IPS and VPN features, a network administrator opens the file realm-cisco.pub.key.txt, and copies and pastes the contents to the router at the global configuration prompt. What is the result after this configuration step?
- The router is authenticated with the Cisco secure IPS resource web server.
- A pair of public/secret keys is created for IPsec VPN operation.
- A crypto key is created for IOS IPS to verify the master signature file.*
- A pair of public/secret keys is created for the router to serve as an SSH server.
-
Refer to the exhibit. Based on the configuration, which traffic will be examined by the IPS that is configured on router R1?
CCNA Security Chapter 5 Exam Answer v2 002
- traffic that is destined to LAN 1 and LAN 2
- return traffic from the web server
- traffic that is initiated from LAN 1 and LAN 2
- no traffic will be inspected*
- http traffic that is initiated from LAN 1
-
Refer to the exhibit. Based on the IPS configuration provided, which conclusion can be drawn?
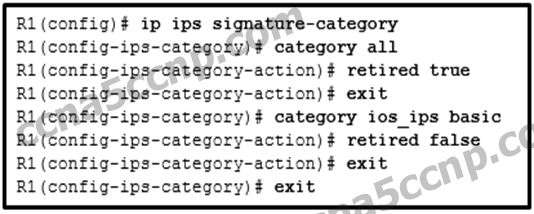
CCNA Security Chapter 5 Exam Answer v2 003
- The signatures in all categories will be compiled into memory and used by the IPS.
- The signatures in all categories will be retired and not be used by the IPS.
- Only the signatures in the ios_ips basic category will be compiled into memory and used by the IPS.*
- The signatures in the ios_ips basic category will be retired and the remaining signatures will be compiled into memory and used by the IPS.
-
What are two shared characteristics of the IDS and the IPS? (Choose two.)
- Both use signatures to detect malicious traffic.*
- Both analyze copies of network traffic.
- Both have minimal impact on network performance.
- Both rely on an additional network device to respond to malicious traffic.
- Both are deployed as sensors.*
-
Refer to the exhibit. A network administrator enters the command on a Cisco IOS IPS router. What is the effect?
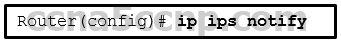
CCNA Security Chapter 5 Exam Answer v2 004
- Alert messages are sent in syslog format.*
- Alert messages are sent in trace file format.
- Alert messages are sent in Security Device Event Exchange (SDEE) format.
- Alert messages are sent in event log format.
-
A network administrator suspects the default setting of the ip ips notify sdee command has caused performance degradation on the Cisco IOS IPS router. The network administrator enters the ip sdee events 50 command in an attempt to remedy the performance issues. What is the immediate effect of this command?
- All events that were stored in the original buffer are saved, while a new buffer is created to store new events.
- All events that were stored in the previous buffer are lost.*
- The newest 50 events from the original buffer are saved and all others are deleted.
- The oldest 50 events of the original buffer are deleted.
-
True or False?
A Cisco IDS does not affect the flow of traffic when it operates in promiscuous mode
- true*
- false
-
What is a required condition to enable IPS activity reporting using the SDEE format?
- Create an IOS IPS configuration directory in flash.
- Enable an HTTP or HTTPS service on the router.*
- Configure the signature category.
- Issue the ip ips notify log command.
-
Refer to the exhibit. Which statement best describes how incoming traffic on serial 0/0 is handled?

CCNA Security Chapter 5 Exam Answer v2 005
- Traffic that is coming from any source other than 172.31.235.0/24 will be scanned and reported.
- Traffic not matching ACL 100 will be dropped.
- Traffic not matching ACL 100 will be scanned and reported.
- Traffic that is sourced from 172.31.235.0/24 will be sent directly to its destination without being scanned or reported.
- Traffic matching ACL 100 will be scanned and reported.*
- Traffic that is sourced from 172.31.235.0/24 will be scanned and reported.
-
A network administrator is configuring an IOS IPS with the command
R1(config)# ip ips signature-definition
Which configuration task can be achieved with this command?
- Retire or unretire the ios_ips basic signature category.
- Retire or unretire an individual signature.*
- Retire or unretire the all signature category.
- Retire or unretire the all atomic signatures category.
-
What are two disadvantages of using an IDS? (Choose two.)
- The IDS analyzes actual forwarded packets.
- The IDS does not stop malicious traffic.*
- The IDS has no impact on traffic.
- The IDS works offline using copies of network traffic.
- The IDS requires other devices to respond to attacks.*
-
What is a disadvantage of network-based IPS as compared to host-based IPS?
- Network-based IPS is less cost-effective.
- Network-based IPS should not be used with multiple operating systems.
- Network-based IPS cannot examine encrypted traffic.*
- Network-based IPS does not detect lower level network events.
-
An IPS sensor has detected the string confidential across multiple packets in a TCP session. Which type of signature trigger and signature type does this describe?
- Trigger: Policy-based detection
Type: Atomic signature - Trigger: Policy-based detection
Type: Composite signature - Trigger: Anomaly-based detection
Type: Atomic signature - Trigger: Anomaly-based detection
Type: Composite signature - Trigger: Pattern-based detection
Type: Atomic signature - Trigger: Pattern-based detection
Type: Composite signature*
- Trigger: Policy-based detection
-
What are two drawbacks to using HIPS? (Choose two.)
- With HIPS, the success or failure of an attack cannot be readily determined.
- With HIPS, the network administrator must verify support for all the different operating systems used inthe network.*
- HIPS has difficulty constructing an accurate network picture or coordinating events that occur across the entire network.*
- If the network traffic stream is encrypted, HIPS is unable to access unencrypted forms of the traffic.
- HIPS installations are vulnerable to fragmentation attacks or variable TTL attacks
