CCNA 4 Pretest Exam Answers
-
Which statement describes a route that has been learned dynamically?
It is identified by the prefix C in the routing table.
It has an administrative distance of 1.
It is automatically updated and maintained by routing protocols.*
It is unaffected by changes in the topology of the network. -
Refer to the exhibit. Which switch will be the root bridge after the election process is complete?
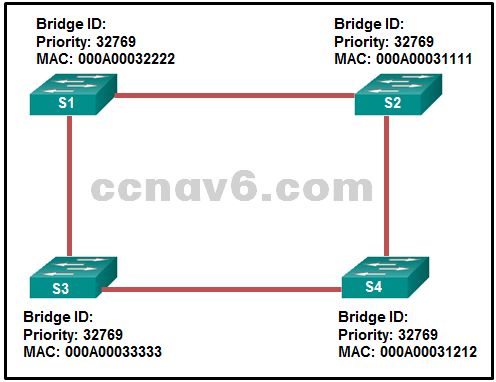
S1
S2*
S3
S4 -
What three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)
DNS*
PPP
ARP
NAT
FTP*
DHCP* -
What important information is examined in the Ethernet frame header by a Layer 2 device in order to forward the data onward?
source MAC address
source IP address
destination MAC address*
destination IP address
Ethernet type -
What are two reasons to implement passive interfaces in the EIGRP configuration of a Cisco router? (Choose two.)
to provide increased network security*
to shut down unused interfaces
to exclude interfaces from load balancing
to avoid unnecessary update traffic*
to mitigate attacks coming from the interfaces -
Which two functions are primary functions of a router? (Choose two.)
packet forwarding*
flow control
microsegmentation
path selection*
domain name resolution -
Which two devices allow hosts on different VLANs to communicate with each other? (Choose two.)
router*
Layer 3 switch*
repeater
Layer 2 switch
hub -
In addition to the cable length, what two factors could interfere with the communication carried over UTP cables? (Choose two.)
bandwidth
electromagnetic interference*
size of the network
crosstalk*
signal modulation technique -
Which information does a switch use to keep the MAC address table information current?
the source MAC address and the incoming port*
the source and destination MAC addresses and the incoming port
the source MAC address and the outgoing port
the destination MAC address and the outgoing port
the source and destination MAC addresses and the outgoing port
the destination MAC address and the incoming port -
The buffers for packet processing and the running configuration file are temporarily stored in which type of router memory?
flash
NVRAM
RAM*
ROM -
How does implementing STP allow for a scalable network design?
It eliminates Layer 2 loops from redundant links.*
It provides failover services when duplicate network equipment is used.
It prevents local traffic from propagating to other parts of the network.
It filters broadcasts and other undesirable traffic from the network. -
A home user is looking for an ISP connection that provides high speed digital transmission over regular phone lines. What ISP connection type should be used?
DSL*
dial-up
satellite
cell modem
cable modem -
What is a characteristic of a default static route?
It uses a single network address to send multiple static routes to one destination address.
It backs up a route already discovered by a dynamic routing protocol.
It identifies the gateway IP address to which the router sends all IP packets for which it does not have a learned or static route.*
It is configured with a higher administrative distance than is the original dynamic routing protocol. -
Which three pairs of trunking modes will establish a functional trunk link between two Cisco switches? (Choose three.)
dynamic desirable – dynamic auto*
dynamic auto – dynamic auto
access – trunk
dynamic desirable – dynamic desirable*
dynamic desirable – trunk*
access – dynamic auto -
On which switch interface would an administrator configure an IP address so that the switch can be managed remotely?
FastEthernet0/1
VLAN 1*
vty 0
console 0 -
A network engineer has been tasked with connecting two large autonomous systems (AS) together over the Internet. Which routing protocol should be selected?
IS-IS
EIGRP
OSPFv2
BGP* -
An EIGRP router loses the route to a network. Its topology table contains two feasible successors to the same network. What action will the router take?
The DUAL algorithm is recomputed to find an alternate route.
The router uses the default route.
The router will query neighbors for an alternate route.
The best alternative backup route is immediately inserted into the routing table.* -
What three blocks of addresses are defined by RFC 1918 for private network use? (Choose three.)
192.168.0.0/16*
169.254.0.0/16
239.0.0.0/8
172.16.0.0/12*
10.0.0.0/8*
100.64.0.0/14 -
Which two pieces of information are required when creating a standard access control list? (Choose two.)
destination address and wildcard mask
access list number between 1 and 99*
access list number between 100 and 199
source address and wildcard mask*
subnet mask and wildcard mask -
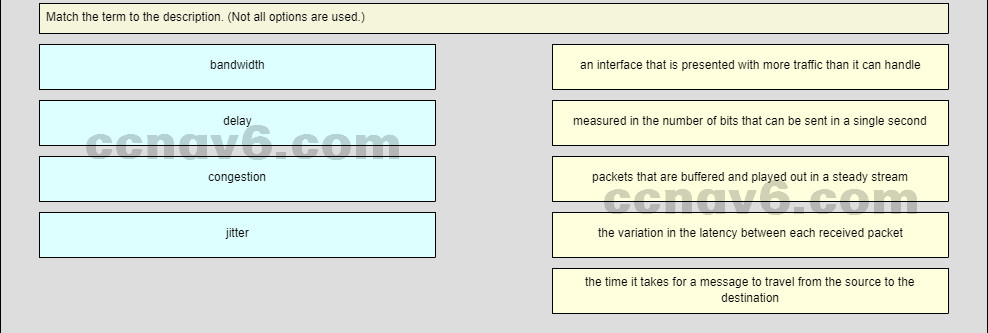
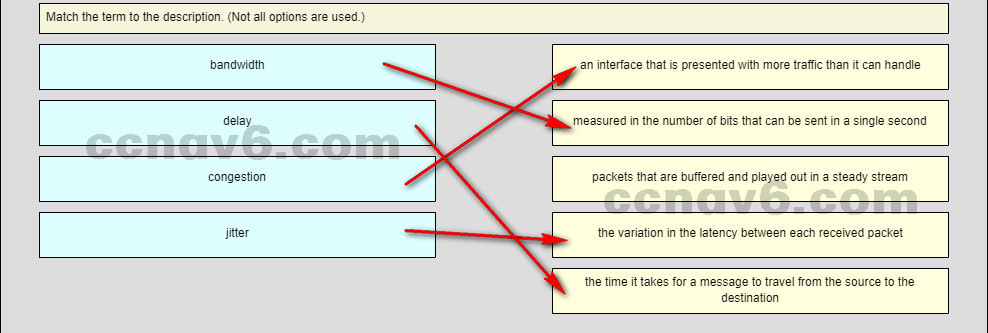
Question as presented:
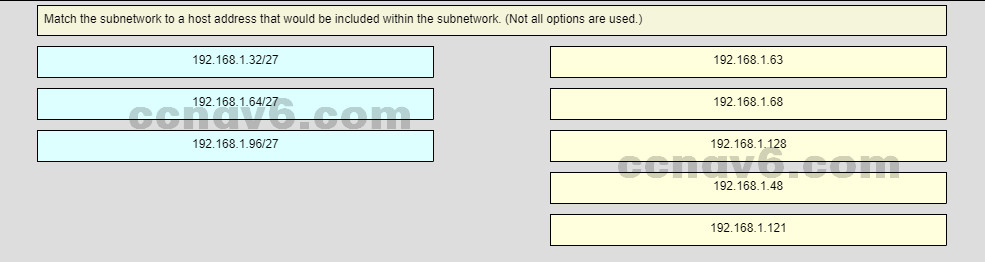
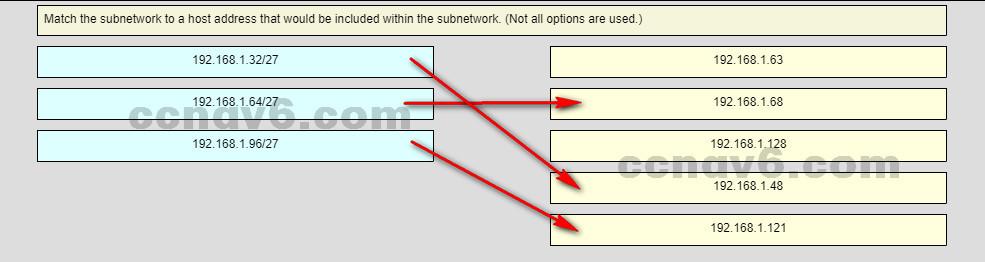
-
Which criterion is preferred by the router to choose a router ID?
the router-id rid command*
the IP address of the highest configured loopback interface on the router
the IP address of the highest active interface on the router
the IP address of the highest active OSPF-enabled interface -
A network administrator is entering the command ipv6 unicast-routing to start configuring DHCPv6 operation on a router. Which statement describes the function of this command?
It is required to configure stateless DHCPv6 server on the router.
It is required to configure stateful DHCPv6 server on the router.
It is required for sending ICMPv6 RA messages.*
It is required for enabling DNS service in DHCPv6 configurations. -
What three services are provided by the transport layer? (Choose three.)
encryption of data
path determination
bit transmission
flow control*
error recovery*
connection establishment*
data representation -
Which TCP/IP model layer is closest to the end user?
internet
transport
application*
network access -
When applied to a router, which command would help mitigate brute-force password attacks against the router?
service password-encryption
login block-for 60 attempts 5 within 60*
exec-timeout 30
banner motd $Max failed logins = 5$ -
Which circumstance would result in an enterprise deciding to implement a corporate WAN?
when its employees become distributed across many branch locations*
when the enterprise decides to secure its corporate LAN
when the network will span multiple buildings
when the number of employees exceeds the capacity of the LAN -
A corporation is searching for an easy and low cost solution to provide teleworkers with a secure connection to headquarters. Which solution should be selected?
leased line connection
site-to-site VPN over the Internet
dial-up connection
remote access VPN over the Internet* -
Which three statements are true about PPP? (Choose three.)
PPP can only be used between two Cisco devices.
PPP uses LCPs to agree on format options such as authentication, compression, and error detection.*
PPP carries packets from several network layer protocols in LCPs.
PPP uses LCPs to establish, configure, and test the data-link connection.*
PPP can use synchronous and asynchronous circuits.* -
A network administrator is configuring a PPP link with the commands:
R1(config-if)# encapsulation ppp
R1(config-if)# ppp quality 70What is the effect of these commands?
The NCP will send a message to the sending device if the link usage reaches 70 percent.
The PPP link will not be established if more than 30 percent of options cannot be accepted.
The LCP establishment phase will not start until the bandwidth reaches 70 percent or more.
The PPP link will be closed down if the link quality drops below 70 percent.* -
What is the protocol that provides ISPs the ability to send PPP frames over DSL networks?
CHAP
ADSL
LTE
PPPoE* -
Refer to the exhibit. All routers are successfully running the BGP routing protocol. How many routers must use EBGP in order to share routing information across the autonomous systems?
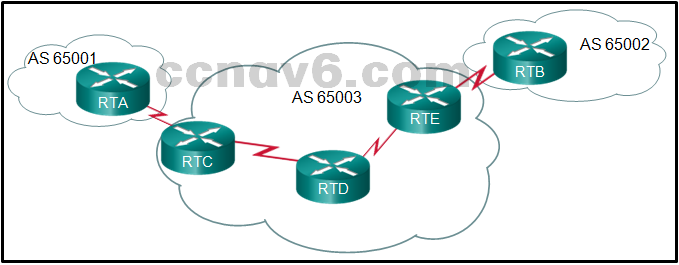
2
4*
5
3 -
Which three values or sets of values are included when creating an extended access control list entry? (Choose three.)
destination subnet mask and wildcard mask
source address and wildcard mask*
source subnet mask and wildcard mask
destination address and wildcard mask*
access list number between 100 and 199*
default gateway address and wildcard mask
access list number between 1 and 99 -
Which pillar of the Cisco IoT System allows data to be analyzed and managed at the location where it is generated?
fog computing*
application enhancement platform
network connectivity
data analytics -
What two protocols are supported on Cisco devices for AAA communications? (Choose two.)
HSRP
RADIUS*
VTP
TACACS+*
LLDP -
What guideline is generally followed about the placement of extended access control lists?
They should be placed as close as possible to the source of the traffic to be denied.*
They should be placed as close as possible to the destination of the traffic to be denied.
They should be placed on the fastest interface available.
They should be placed on the destination WAN link. -
What network monitoring tool copies traffic moving through one switch port, and sends the copied traffic to another switch port for analysis?
SPAN*
SNMP
syslog
802.1X -
Question as presented:
-
Which type of QoS marking is applied to Ethernet frames?
DSCP
CoS*
ToS
IP precedence -
Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior?
debug output and packet captures
network configuration files
the network performance baseline*
syslog records and messages -
Which feature sends simulated data across the network and measures performance between multiple network locations?
IP SLA*
LLDP
SPAN
syslog
