CCNA 2 Practice Final Exam Answers
-
The buffers for packet processing and the running configuration file are temporarily stored in which type of router memory?
flash
NVRAM
RAM*
ROM -
Refer to the exhibit. A company has an internal network of 192.168.10.0/24 for their employee workstations and a DMZ network of 192.168.3.0/24 to host servers. The company uses NAT when inside hosts connect to outside network. A network administrator issues the show ip nat translations command to check the NAT configurations. Which one of source IPv4 addresses is translated by R1 with PAT?
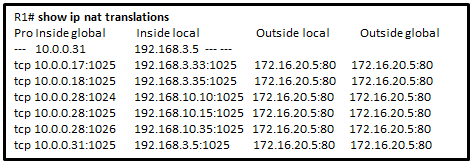
10.0.0.31
192.168.3.5
192.168.3.33
192.168.10.35*
172.16.20.5 -
Refer to the exhibit. This network has two connections to the ISP, one via router C and one via router B. The serial link between router A and router C supports EIGRP and is the primary link to the Internet. If the primary link fails, the administrator needs a floating static route that avoids recursive route lookups and any potential next-hop issues caused by the multiaccess nature of the Ethernet segment with router B. What should the administrator configure?

Create a static route pointing to Fa0/0 with an AD of 1.
Create a static route pointing to 10.1.1.1 with an AD of 95.
Create a static route pointing to 10.1.1.1 with an AD of 1.
Create a fully specified static route pointing to Fa0/0 with an AD of 1.*
Create a fully specified static route pointing to Fa0/0 with an AD of 95. -
Which type of inter-VLAN communication design requires the configuration of multiple subinterfaces?
legacy inter-VLAN routing
routing for the management VLAN
router on a stick*
routing via a multilayer switch -
After sticky learning of MAC addresses is enabled, what action is needed to prevent dynamically learned MAC addresses from being lost in the event that an associated interface goes down?
Reboot the switch.
Copy the running configuration to the startup configuration.*
Shut down the interface then enable it again with the no shutdown command.
Configure port security for violation protect mode. -
A network technician is configuring port security on switches. The interfaces on the switches are configured in such a way that when a violation occurs, packets with unknown source addresses are dropped and no notification is sent. Which violation mode is configured on the interfaces?
off
restrict
protect*
shutdown -
A technician is configuring a switch to allow access both to IP phones and to PCs on interface Fa0/12. The technician enters the interface command mls qos trust cos. What is the reason for including that command?
It is used in conjuction with STP PortFast to ensure that interface Fa0/12, in case of a shutdown, regains an “up” state immediately.
It is used to verify service levels and to ensure that congestion over serial interfaces is minimized for voice traffic.
It is used to set the trusted state of an interface to allow classification of traffic for QoS based on the CoS value of the IP phone.*
It is used to provide higher categories of security for voice and video traffic. -
What is the minimum configuration for a router interface that is participating in IPv6 routing?
to have only a link-local IPv6 address*
to have both a link-local and a global unicast IPv6 address
to have both an IPv4 and an IPv6 address
to have a self-generated loopback address
to have only an automatically generated multicast IPv6 address -
Refer to the exhibit. Assuming that the routing tables are up to date and no ARP messages are needed, after a packet leaves H1, how many times is the L2 header rewritten in the path to H2?
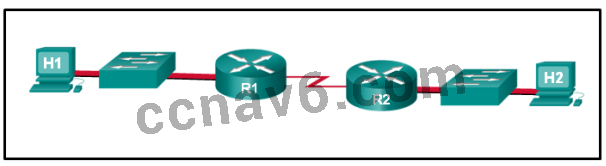
1
2*
3
4
5
6 -
What command will enable a router to begin sending messages that allow it to configure a link-local address without using an IPv6 DHCP server?
a static route
the ipv6 route ::/0 command
the ipv6 unicast-routing command*
the ip routing command -
Which switching method provides error-free data transmission?
- fragment-free
- fast-forward
- integrity-checking
- store-and-forward*
-
Which problem is evident if the show ip interface command shows that the interface is down and the line protocol is down?
A cable has not been attached to the port.*
There is an IP address conflict with the configured address on the interface.
The no shutdown command has not been issued on the interface.
An encapsulation mismatch has occurred. -
A company security policy requires that all MAC addressing be dynamically learned and added to both the MAC address table and the running configuration on each switch. Which port security configuration will accomplish this?
auto secure MAC addresses
dynamic secure MAC addresses
static secure MAC addresses
sticky secure MAC addresses* -
Refer to the exhibit. A small business uses VLANs 8, 20, 25, and 30 on two switches that have a trunk link between them. What native VLAN should be used on the trunk if Cisco best practices are being implemented?
1
5*
8
20
25
30 -
A network administrator is configuring an ACL with the command access-list 10 permit 172.16.32.0 0.0.15.255. Which IPv4 address matches the ACE?
172.16.20.2
172.16.26.254
172.16.45.2*
172.16.48.5 -
The PT initialization was skipped. You will not be able to view the PT activity.
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question.
Which code is displayed on the web browser?Inter-VLANonfigured!
It works!*
Welldone!
Grea -
Which command is issued in the VTY line configuration mode to apply a standard ACL that will control Telnet access to a router?
access-group 11 in
access-class 11 in*
access-list 11 in
access-list 110 in -
Which series of commands will cause access list 15 to restrict Telnet access on a router?
R1(config)# line vty 0 4
R1(config-line)# ip access-group 15 inR1(config)# int gi0/0
R1(config-if)# ip access-group 15 inR1(config)# line vty 0 4
R1(config-line)# access-class 15 in*R1(config)# int gi0/0
R1(config-if)# access-class 15 inOnce an access list to restrict Telnet or SSH access has been created, it is applied to the vty lines with the access-class command. This will restrict Telnet or SSH access.
-
Which three statements accurately describe VLAN types? (Choose three).
A management VLAN is any VLAN that is configured to access management features of the switch.*
A data VLAN is used to carry VLAN management data and user-generated traffic.
Voice VLANs are used to support user phone and e-mail traffic on a network.
VLAN 1 is always used as the management VLAN.
After the initial boot of an unconfigured switch, all ports are members of the default VLAN.*
An 802.1Q trunk port, with a native VLAN assigned, supports both tagged and untagged traffic.* -
A client is using SLAAC to obtain an IPv6 address for its interface. After an address has been generated and applied to the interface, what must the client do before it can begin to use this IPv6 address?
- It must send a DHCPv6 INFORMATION-REQUEST message to request the address of the DNS server.
- It must send an ICMPv6 Router Solicitation message to determine what default gateway it should use.
- It must send a DHCPv6 REQUEST message to the DHCPv6 server to request permission to use this address.
- It must send an ICMPv6 Neighbor Solicitation message to ensure that the address is not already in use on the network.*
-
Which DHCP IPv4 message contains the following information?
Destination address: 255.255.255.255
Client IPv4 address: 0.0.0.0
Default gateway address: 0.0.0.0
Subnet mask: 0.0.0.0- DHCPACK
- DHCPDISCOVER*
- DHCPOFFER
- DHCPREQUEST
-
A network administrator is implementing DHCPv6 for the company. The administrator configures a router to send RA messages with M flag as 1 by using the interface command ipv6 nd managed-config-flag. What effect will this configuration have on the operation of the clients?
Clients must use the information that is contained in RA messages.
Clients must use all configuration information that is provided by a DHCPv6 server.*
Clients must use the prefix and prefix length that are provided by RA messages and obtain additional information from a DHCPv6 server.
Clients must use the prefix and prefix length that are provided by a DHCPv6 server and generate a random interface ID. -
Refer to the exhibit. The users on the LAN network of R1 cannot receive an IPv6 address from the configured stateful DHCPv6 server. What is missing from the stateful DHCPv6 configuration on router R1?
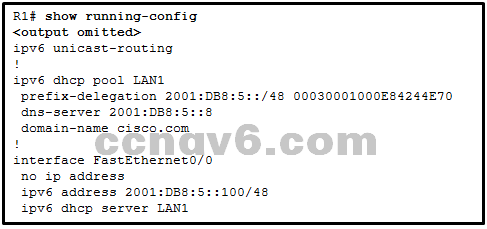
The FA0/0 interface is missing the command that informs the clients to use stateful DHCPv6.*
IPv6 has not been enabled globally on router R1.
The DHCPv6 pool has not been bound to the LAN interface.
The DHCPv6 pool does not match the IPv6 address configured on interface FA0/0. -
Refer to the exhibit. NAT is configured on R1 and R2. The PC is sending a request to the web server. What IPv4 address is the source IP address in the packet between R2 and the web server?
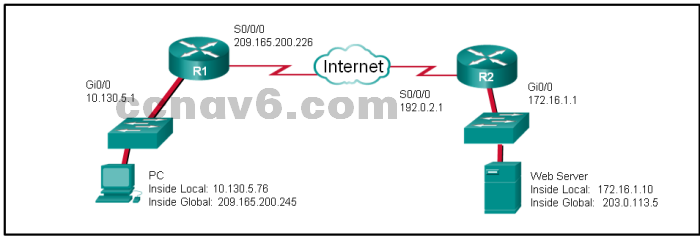
10.130.5.76
209.165.200.245*
172.16.1.10
203.0.113.5
192.0.2.1
172.16.1.1 -
Refer to the exhibit. R1 is configured for NAT as displayed. What is wrong with the configuration?
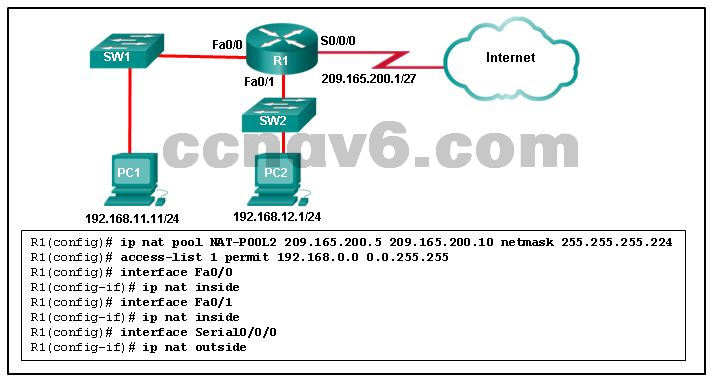
NAT-POOL2 is not bound to ACL 1.*
Interface Fa0/0 should be identified as an outside NAT interface.
The NAT pool is incorrect.
Access-list 1 is misconfigured. -
A network engineer is configuring PAT on a router and has issued the command:
ip nat source list 1 interface serial 0/1/0 overload
Which additional command is required to specify addresses from the 192.168.128.0/18 network as the inside local addresses?ip nat inside source list 1 pool INSIDE_NAT_POOL
access-list 1 permit 192.168.128.0 0.0.127.255
access-list 1 permit 192.168.128.0 255.255.192.0
access-list 1 permit 192.168.128.0 0.0.63.255*
ip nat inside source static 192.168.128.0 209.165.200.254 -
Refer to the exhibit. If the IP addresses of the default gateway router and the DNS server are correct, what is the configuration problem?
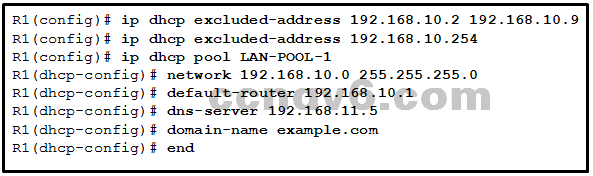
- The DNS server and the default gateway router should be in the same subnet.
- The IP address of the default gateway router is not contained in the excluded address list.*
- The default-router and dns-server commands need to be configured with subnet masks.
- The IP address of the DNS server is not contained in the excluded address list.
-
Fill in the blank.
In IPv6, all routes are level ___ ultimate routes.
Correct Answer: 1*
-
Fill in the blank.
The acronym ___ describes the type of traffic that requires a separate VLAN, strict QoS requirements, and a one-way overall delay less than 150 ms across the network. These restrictions help to ensure traffic quality.
Correct Answer: voip*
-
Refer to the exhibit. A network administrator has just configured address translation and is verifying the configuration. What three things can the administrator verify? (Choose three.)
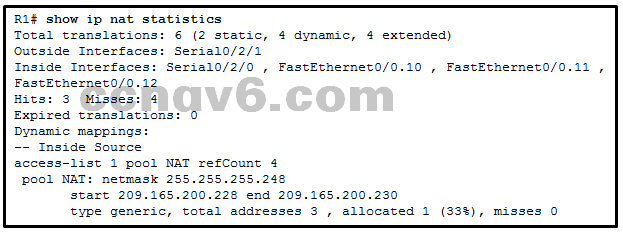
- Address translation is working.*
- Three addresses from the NAT pool are being used by hosts.
- The name of the NAT pool is refCount.
- A standard access list numbered 1 was used as part of the configuration process.*
- Two types of NAT are enabled.*
- One port on the router is not participating in the address translation.
-
Which destination do Cisco routers and switches use by default when sending syslog messages for all severity levels?
NVRAM
nearest syslog server
console*
RAM -
Which requirement should be checked before a network administrator performs an IOS image upgrade on a router?
The desired IOS image file has been downloaded to the router.
There is sufficient space in flash memory.*
The old IOS image file has been deleted.
The FTP server is operational. -
A network administrator configures a router with the command sequence:
R1(config)# boot system tftp://c1900-universalk9-mz.SPA.152-4.M3.bin R1(config)# boot system rom
What is the effect of the command sequence?
The router will load IOS from the TFTP server. If the image fails to load, it will load the IOS image from ROM.*
The router will search and load a valid IOS image in the sequence of flash, TFTP, and ROM.
The router will copy the IOS image from the TFTP server and then reboot the system.
On next reboot, the router will load the IOS image from ROM. -
Which three software packages are available for Cisco IOS Release 15.0?
Unified Communications*
DATA*
Enterprise Services
Advanced IP Services
IPVoice
Security* -
What two license states would be expected on a new Cisco router once the license has been activated? (Choose two.)
License State: Active, In Use*
License State: Active, Registered
License Type: ipbasek9
License Type: Temporary
License State: On
License Type: Permanent* -
Which type of static route typically uses the distance parameter in the ip route global configuration command?
- summary static route
- default static route
- floating static route*
- standard static route
-
Refer to the exhibit. Which type of IPv6 static route is configured in the exhibit?
fully specified static route
recursive static route*
directly attached static route
floating static route -
Refer to the exhibit. Which route was configured as a static route to a specific network using the next-hop address?
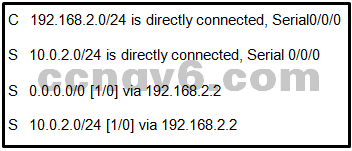
C 192.168.2.0/24 is directly connected, Serial0/0/0
S 0.0.0.0/0 [1/0] via 192.168.2.2
S 10.0.2.0/24 [1/0] via 192.168.2.2*
S 10.0.2.0/24 is directly connected, Serial 0/0/0 -
A network administrator has entered the following command:
ip route 192.168.10.64 255.255.255.192 serial0/0/1
When the network administrator enters the command show ip route, the route is not in the routing table. What should the administrator do next?
Re-enter the command using a network number rather than a usable IP address.
Verify that the serial 0/0/1 interface is active and available.*
Re-enter the command using the correct mask.
Verify that the 192.168.10.64 network is active within the network infrastructure. -
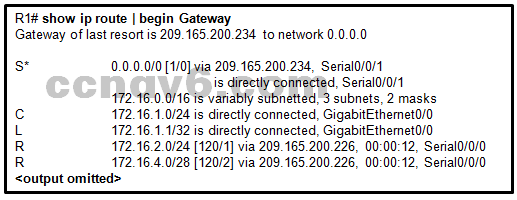
Refer to the exhibit. How did the router obtain the last route that is shown?
The ip route command was used.
The ipv6 route command was used.
Another router in the same organization provided the default route by using a dynamic routing protocol.*
The ip address interface configuration mode command was used in addition to the network routing protocol configuration mode command. -
To enable RIP routing for a specific subnet, the configuration command network 192.168.5.64 was entered by the network administrator. What address, if any, appears in the running configuration file to identify this network?
192.168.5.64
192.168.5.0*
192.168.0.0
No address is displayed. -
Refer to the exhibit. What is the administrative distance value that indicates the route for R2 to reach the 10.10.0.0/16 network?

1*
120
0
2 -
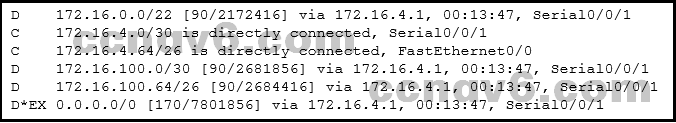
Refer to the exhibit. Which type of route is 172.16.0.0/16?
ultimate route
level 1 parent route*
child route
default route -
What is the name of the layer in the Cisco borderless switched network design that would have more switches deployed than other layers in the network design of a large organization?
data link
core
network access
access*
network -
What is a function of the distribution layer?
high-speed backbone connectivity
interconnection of large-scale networks in wiring closets*
network access to the user
fault isolation -
Which network design principle focuses on the capability of on-demand seamless network expansion in a switched network?
flexibility
modularity*
resiliency
hierarchical -
A lab in a network management software company is configuring a testing environment to verify the performance of new software with different network connectivity speeds, including FastEthernet, GigabitEthernet, and 10 GigabitEthernet, and with copper and fiber optic connections. Which type of switch should the software company purchase to perform the tests?
fixed configuration
access layer
modular configuration*
stackable -
What information is added to the switch table from incoming frames?
destination MAC address and incoming port number
destination IP address and incoming port number
source MAC address and incoming port number*
source IP address and incoming port number -
Which statement correctly describes how a LAN switch forwards frames that it receives?
Cut-through frame forwarding ensures that invalid frames are always dropped.
Only frames with a broadcast destination address are forwarded out all active switch ports.
Frame forwarding decisions are based on MAC address and port mappings in the CAM table.*
Unicast frames are always forwarded regardless of the destination MAC address.
