12.5.13 Packet Tracer – Troubleshoot Enterprise Networks (Instructor Version)
Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only.
Objectives
- Part 1: Verify Switching Technologies
- Part 2: Verify DHCP
- Part 3: Verify Routing
- Part 4: Verify WAN Technologies
- Part 5: Verify Connectivity
Scenario
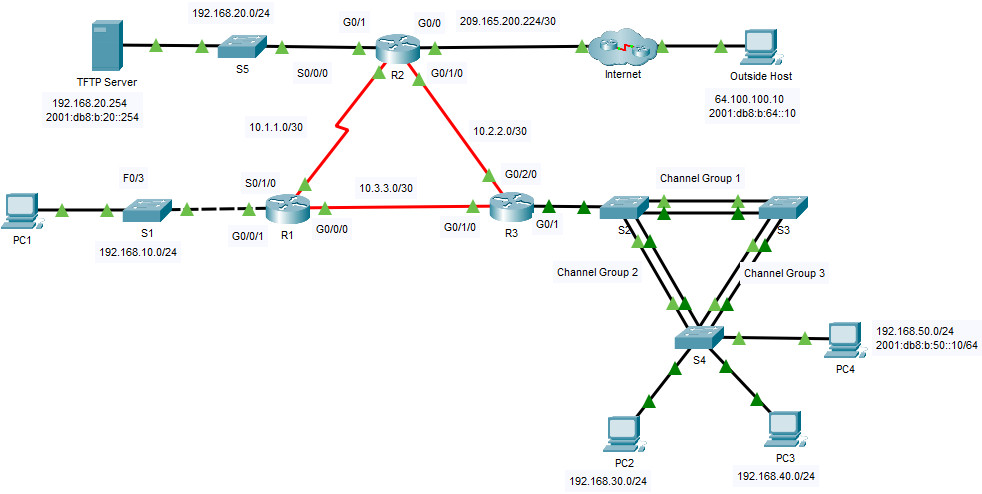
This activity uses a variety of technologies that you have encountered during your CCNA studies, including IPv4 routing, IPv6 routing, port security, EtherChannel, DHCP, and NAT. Your task is to review the requirements, isolate and resolve any problems, and then document the steps you took to verify the requirements.
The company replaced routers R1 and R3 to accommodate a fiber connection between the locations. Configurations from the previous routers with serial connections were modified and applied as a starting configuration. IPv6 is being tested on a small portion of the network and needs to be verified.
Note: Passwords have been removed for ease of troubleshooting in this exercise. The typical password protections should be reapplied; however, the activity will not grade those items.
Addressing Table
| Device | Interface | IP Address / Prefix | Default Gateway |
|---|---|---|---|
| R1 | G0/0/1 | 192.168.10.1 /24 | N/A |
| S0/1/0 | 10.1.1.1 /30 | N/A | |
| G0/0/0 | 10.3.3.1 /30 | N/A | |
| R2 | G0/0 | 209.165.200.225 /27 | N/A |
| 2001:db8:b:209::1/64 | |||
| G0/1 | 192.168.20.1 /30 | N/A | |
| 2001:db8:b:20::1/64 | |||
| S0/0/0 | 10.1.1.2 /30 | N/A | |
| G0/1/0 | 10.2.2.1 /30 | N/A | |
| 2001:db8:b:10:2::1/64 | |||
| R3 | G0/1.30 | 192.168.30.1 /24 | N/A |
| G0/1.40 | 192.168.40.1 /24 | N/A | |
| G0/1.50 | 192.168.50.1 /24 | N/A | |
| 2001:db8:b:50::1/64 | |||
| G0/1.99 | N/A | N/A | |
| G0/1/0 | 10.3.3.2 /30 | N/A | |
| G0/2/0 | 10.2.2.2 /30 | N/A | |
| 2001:db8:b:10:2::2/64 | |||
| S1 | VLAN10 | 192.168.10.2 /24 | 192.168.10.1 |
| S2 | VLAN11 | 192.168.99.2 /24 | N/A |
| S3 | VLAN30 | 192.168.99.3 /24 | N/A |
| S4 | VLAN30 | 192.168.99.4 /24 | N/A |
| PC1 | NIC | IPv4 DHCP assigned | IPv4 DHCP assigned |
| PC2 | NIC | IPv4 DHCP assigned | IPv4 DHCP assigned |
| PC3 | NIC | IPv4 DHCP assigned | IPv4 DHCP assigned |
| PC4 | NIC | IPv4 DHCP assigned | IPv4 DHCP assigned |
| 2001:db8:b:50::10/64 | fe80::3 | ||
| TFTP Server | NIC | 192.168.20.254 /24 | 192.168.20.1 |
| 2001:db8:b:20::254/64 | fe80::2 |
Instructions
Part 1: Verify Switching Technologies
a. Port security is configured to only allow PC1 to access S1’s F0/3 interface. All violations should disable the interface.
Issue the command on S1 to display the current port security status.
S1# show port-security
b. Enter interface configuration mode for interface F0/3 and set up port security.
S1(config)# interface f0/3
S1(config-if)# switchport port-security
S1(config-if)# switchport port-security mac-address sticky
c. Devices in the LAN on S1 should be in VLAN 10. Display the current state of VLAN configuration.
S1#show vlan
VLAN Name Status Ports
---- -------------------------------- --------- -------------------------------
1 default active Fa0/1, Fa0/2, Fa0/5, Fa0/6
Fa0/7, Fa0/8, Fa0/9, Fa0/10
Fa0/11, Fa0/12, Fa0/13, Fa0/14
Fa0/15, Fa0/16, Fa0/17, Fa0/18
Fa0/19, Fa0/20, Fa0/21, Fa0/22
Fa0/23, Fa0/24, Gig0/1, Gig0/2
10 V10 active Fa0/3, Fa0/4
1002 fddi-default active
1003 token-ring-default active
1004 fddinet-default active
1005 trnet-default active
What ports are currently assigned to VLAN 10?
d. PC1 should be receiving an IP address from the router R1.
Does the PC currently have an IP address assigned?
e. Notice the G0/1 interface on R1 is not in the same VLAN as PC1. Change the G0/1 interface to be a member of VLAN 10 and set portfast on the interface.
S1(config-if)# int G0/1 S1(config-if)# switchport access vlan 10 S1(config-if)# spanning-tree portfast
f. Reset the interface address on PC1 from the GUI or by using the command prompt and the ipconfig /renew command. Does PC1 have an address? Yes, IP is 192.168.10.10 If not, recheck your steps. Test connectivity to the TFTP Server. The ping should be successful.
g. The LAN connected to R3 had an additional switch added to the topology. Link aggregation using EtherChannel is configured on S2, S3, and S4. The EtherChannel links should be set to trunk. The EtherChannel links should be set to form a channel without using a negotiation protocol. Issue the command on each switch to determine if the channel is working correctly.
S2# show etherchannel summary <output omitted> 1 Po1(SU) - Fa0/1(P) Fa0/2(P) 2 Po2(SU) - Fa0/3(P) Fa0/4(P)
Were there any problems with EtherChannel?
h. Modify S3 to include ports F0/1 and F0/2 as port channel 1.
S3(config)# interface range f0/1-2 S3(config-if-range)# channel-group 1 mode on
Check the status of the EtherChannel on S3. It should be stable now. If it is not, check the previous steps.
i. Verify the trunk status on all switches.
S3# show int trunk
Were there any issues with trunking?
j. Correct the trunk issues on S2.
S2(config)# int g0/1 S2(config-if)# switchport trunk native vlan 99
k. Spanning Tree should be set to PVST+ on S2, S3, and S4. S2 should be configured to be the root bridge for all VLANs. Issue the command to display the spanning-tree status on S2.
S2# show spanning-tree summary totals Switch is in pvst mode Root bridge for:
l. The command output shows that S2 is not the root bridge for any VLANs. Correct the spanning-tree status on S2.
S2(config)# spanning-tree vlan 1-1005 root primary
m. Check the spanning-tree status on S2 to verify the changes.
S2# show spanning-tree summary totals Switch is in pvst mode Root bridge for: default V30 V40 V50 Native
Part 2: Verify DHCP
- R1 is the DHCP server for the R1 LAN.
- R3 is the DHCP server for all 3 LANs attached to R3.
a. Check the addressing of the PCs.
Do they all have correct addressing?
b. Check the DHCP settings on R3. Filter the output from the show run command to start with the DHCP configuration.
R3# sh run | begin dhcp ip dhcp excluded-address 192.168.30.1 192.168.30.9 ip dhcp excluded-address 192.168.40.1 192.168.40.9 ip dhcp excluded-address 192.168.50.1 192.168.50.9 ! ip dhcp pool LAN30 network 192.168.30.0 255.255.255.0 default-router 192.168.30.1 ip dhcp pool LAN40 network 192.168.40.0 255.255.255.0 default-router 192.168.30.1 ip dhcp pool LAN50 network 192.168.50.0 255.255.255.0 default-router 192.168.30.1
Are there any issues with the DHCP configurations?
c. Make any necessary corrections and reset the IP addresses on the PCs. Check connectivity to all devices.
R3(config)#ip dhcp pool LAN40
R3(dhcp-config)#network 192.168.40.0 255.255.255.0
R3(dhcp-config)#default-router 192.168.40.1
R3(dhcp-config)#ip dhcp pool LAN50
R3(dhcp-config)#network 192.168.50.0 255.255.255.0
R3(dhcp-config)#default-router 192.168.50.1
ipconfig /renew command.Were you able to ping all IPv4 addresses?
Part 3: Verify Routing
Verify that the following requirements have been met. If not, complete the configurations.
- All routers are configured with OSPF process ID 1 and no routing updates should be sent across interfaces that do not have routers connected.
R3(config)#router ospf 1
R3(config-router)#passive-interface g0/1.30
R3(config-router)#passive-interface g0/1.40
R3(config-router)#passive-interface g0/1.50
a. Check the routing tables on all routers.
R3# show ip route ospf
<output omitted>
10.0.0.0/8 is variably subnetted, 5 subnets, 2 masks
O 10.1.1.0 [110/649] via 10.2.2.1, 01:15:53, GigabitEthernet0/2/0
O 192.168.10.0 [110/649] via 10.3.3.1, 01:15:53, GigabitEthernet0/1/0
192.168.20.0 [110/2] via 10.2.2.1, 01:15:53, GigabitEthernet0/2/0
<output omitted>
Do all of the networks appear on all routers?
b. Ping the Outside Host from R2.
Was the ping successful?
c. Correct the default route propagation.
R2(config)# router ospf 1 R2(config-router)# default-information originate
d. Check the routing tables on R1 and R3 to make certain the default route is present.
e. Test IPv6 connectivity from R2 to Outside Host and TFTP Server. The pings should be successful. Troubleshoot if they are not.
f. Test IPv6 connectivity from R2 to PC4. If the ping fails be sure to check that the IPv6 addressing matches the Addressing Table.
g. Test IPv6 connectivity from R3 to Outside Host. If the ping fails, check the IPv6 routes on R3. Be sure to validate the default route originating from R2. If the route does not appear, modify the IPv6 OSPF configuration on R2.
R2(config)# ipv6 router ospf 1 R2(config-rtr)# default-information originate
h. Check connectivity from R2 to Outside Host. The ping should be successful.
Part 4: Verify WAN Technologies
- The serial link between R1 and R2 is used as a backup link in case of failure and should only carry traffic if the fiber link is unavailable.
- The Ethernet link between R2 and R3 is a fiber connection.
- The Ethernet link between R1 and R3 is a fiber connection and should be used to forward traffic from R1.
a. Take a close look at the routing table on R1.
Are there any routes using the serial link?
Use the traceroute command to verify any suspicious paths.
R1# traceroute 192.168.20.254 Type escape sequence to abort. Tracing the route to 192.168.20.254 1 10.1.1.2 1 msec 1 msec 1 msec 2 192.168.20.254 1 msec 9 msec 0 msec
Notice the traffic is being sent via the S0/1/0 interface as opposed to the G0/0/0 interface.
b. The original configurations that came from the previous serial WAN connections were transferred to the new devices. Compare the G0/0/0 interface and Serial0/1/0 interface settings. Notice they both have an OSPF cost value set. Remove the OSPF cost setting from the G0/0/0 interface. It will also be necessary to remove the setting on the link on R3 that connects to R1.
R1(config)# int g0/0/0 R1(config-if)# no ip ospf cost 648
R3(config)# int g0/1/0 R3(config-if)# no ip ospf cost 648
c. Reissue the traceroute command from R1 to verify that the path has changed.
d. The change has been made to direct traffic over the faster link, however the backup route needs to be tested. Shut down the G0/2/0 interface on R3 and test connectivity to the TFTP Server and Outside Host.
Were the pings successful?
e. R2 is required to perform NAT for all internal networks. Check the NAT translations on R2.
R2# show ip nat translations
f. Notice that the list is empty if you have only attempted to ping from R1. Attempt a ping from R3 to Outside Host and recheck the NAT translations on R2. Issue the command to display the current NAT statistics which will also provide the interfaces involved in NAT.
R2# show ip nat statistics <output will vary> Total translations: 0 (0 static, 0 dynamic, 0 extended) Outside Interfaces: GigabitEthernet0/0 Inside Interfaces: GigabitEthernet0/1 , GigabitEthernet0/1/0 Hits: 17 Misses: 27 Expired translations: 17 Dynamic mappings:
g. Set the Serial 0/0/0 interface as an inside interface to translate addresses.
R2(config)# int s0/0/0 R2(config-if)# ip nat inside
h. Test connectivity to Outside Host from R1. The ping should now be successful. Re-enable the G0/2/0 interface on R3.
Part 5: Verify Connectivity
- Devices should be configured according to the Addressing Table.
- Every device should be able to ping every other device internally. The internal PCs should be able to ping the Outside Host.
- PC4 should be able to ping the TFTP Server and the Outside Host using IPv6.
Device Config
S1
enable config terminal interface f0/3 switchport port-security switchport port-security mac-address sticky interface g0/1 switchport access vlan 10 spanning-tree portfast
S3
enable config terminal interface range f0/1-2 channel-group 1 mode on
S2
enable config terminal int g0/1 switchport trunk native vlan 99 spanning-tree vlan 1-1005 root primary
R3
enable config terminal router ospf 1 passive-interface g0/1.30 passive-interface g0/1.40 passive-interface g0/1.50 ip dhcp pool LAN40 network 192.168.40.0 255.255.255.0 default-router 192.168.40.1 ip dhcp pool LAN50 network 192.168.50.0 255.255.255.0 default-router 192.168.50.1 int g0/1/0 no ip ospf cost 648
R2
enable config terminal router ospf 1 default-information originate ipv6 router ospf 1 default-information originate int s0/0/0 ip nat inside
R1
enable config terminal int g0/0/0 no ip ospf cost 648
Download Packet Tracer Completed File
[sociallocker id=”54558″]
[wpdm_package id=’55980′]
[wpdm_package id=’55979′]
[/sociallocker]
[alert-note][one_half]
Previous Lab
11.5.1 Packet Tracer – Compare Layer 2 and Layer 3 Devices
[/one_half][one_half_last]
Next Lab
12.6.1 Packet Tracer – Troubleshooting Challenge – Document the Network
[/one_half_last][/alert-note]
